Databricks and the Security Breach That Almost Happened
Databricks wants you to ask yourself, “Is there a hole in my bucket?”
When the Databricks security engineers were alerted to a possible non-public object in a publicly accessible S3 bucket, the data platform company took it as an opportunity to shore up their cloud. That was, of course, after they breathed a huge sigh of relief that the potential breach proved benign!
Determined to prevent future insecurities, Databricks sought to answer three questions:
- Had any existing objects not intended for public access crept into any of their intentionally public buckets?
- What guardrails could they put in place to ensure private buckets — and their contents — remain private?
- How could they keep an eye out for secrets accidentally placed in public buckets, and receive appropriate notification?
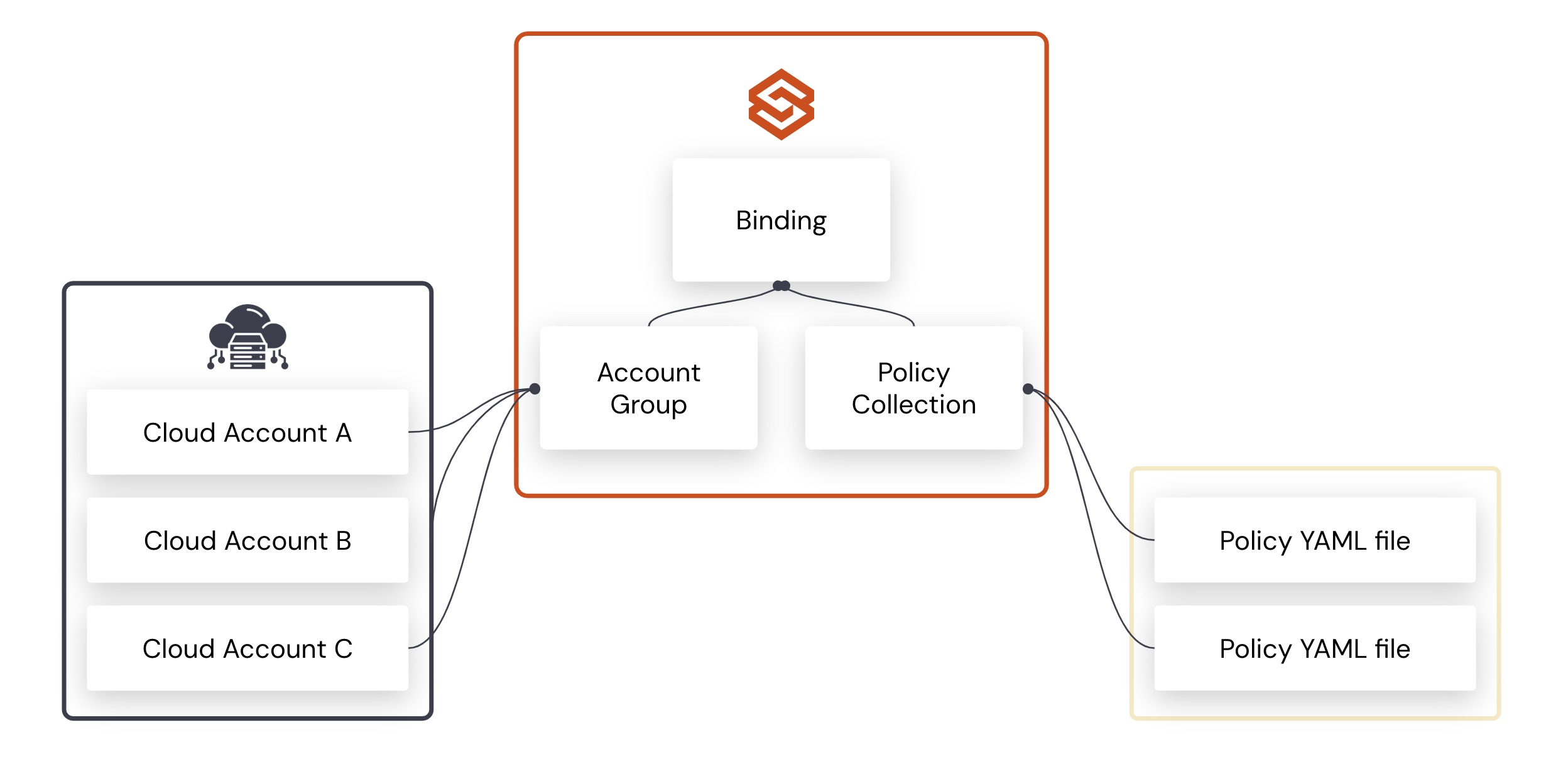
Security engineer Adam Youngberg walks us through Databricks’ answers to these questions. To answer their second question about preventing private objects from going public, Databricks implemented Cloud Custodian.
The source content of this post was written by Adam Youngberg, and appeared in the Databricks blog.
Categories
- cloud-custodian
- use-case