Establish Continuous Visibility and Enforcement of CIS Benchmarks with Stacklet
Industry benchmarks, such as those established by the Center for Internet Security (CIS), provide organizations with best practices for assessing and improving the security of cloud-based infrastructures. CIS is a consensus-driven and unbiased organization. Many organizations use CIS benchmarks and controls to get started on establishing their security and compliance implementations. In addition, once teams have CIS benchmarks in place, they also get a head start in meeting other compliance standards, such as SOC 2 and the Payment Card Industry Data Security Standard (PCI DSS).
While CIS benchmarks provide an excellent opportunity to establish security, it can get challenging and overwhelming for teams to adopt and maintain compliance with these standards. This is true for the following reasons:
- The effort associated with understanding and implementing these policies across multiple clouds and application teams is time-consuming.
- The benchmarks themselves are periodically updated to meet changing regulations and requirements, which means teams may need to revise controls or implement additional policies.
- Further, if application teams make configuration errors in deployment, implementations will often fail to comply with benchmarks. It takes a lot of cycles to track compliance, inform or educate DevOps teams about issues, and eventually remediate issues, particularly across multiple cloud platforms.
With Stacklet Platform, your teams can leverage the insights and guardrails that make it easy to comply with CIS benchmarks. Stacklet Platform is a governance as code solution based on the open-source Cloud Custodian project. With the platform, you can apply policies across multiple public cloud infrastructures, such as Amazon Web Services (AWS) and Microsoft Azure. Stacklet Platform reduces the operational complexity of policy implementation and enables teams to ensure continuous compliance with CIS benchmarks.
Rapidly Assess Your Environment for Non-Compliance with CIS
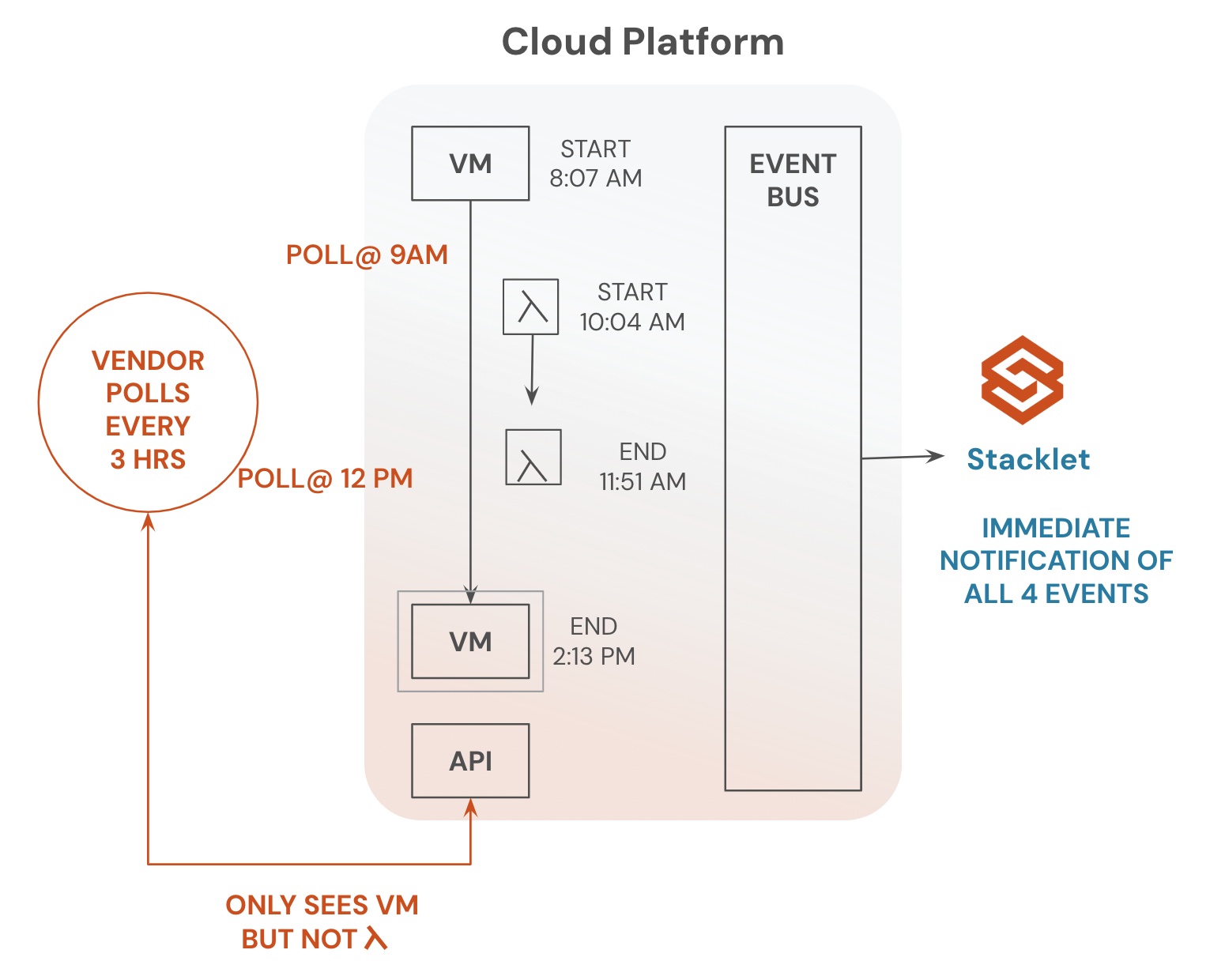
Stacklet Platform automatically discovers and builds a real-time asset database of your cloud resources and configurations. You can easily group accounts by business unit or application groups. Stacklet Platform comes with out-of-the-box policies for CIS benchmarks. Once the policies from the CIS collection get deployed, Stacklet Platform correlates policy results with your cloud estate and builds a dashboard that enables you to view your CIS compliance posture.
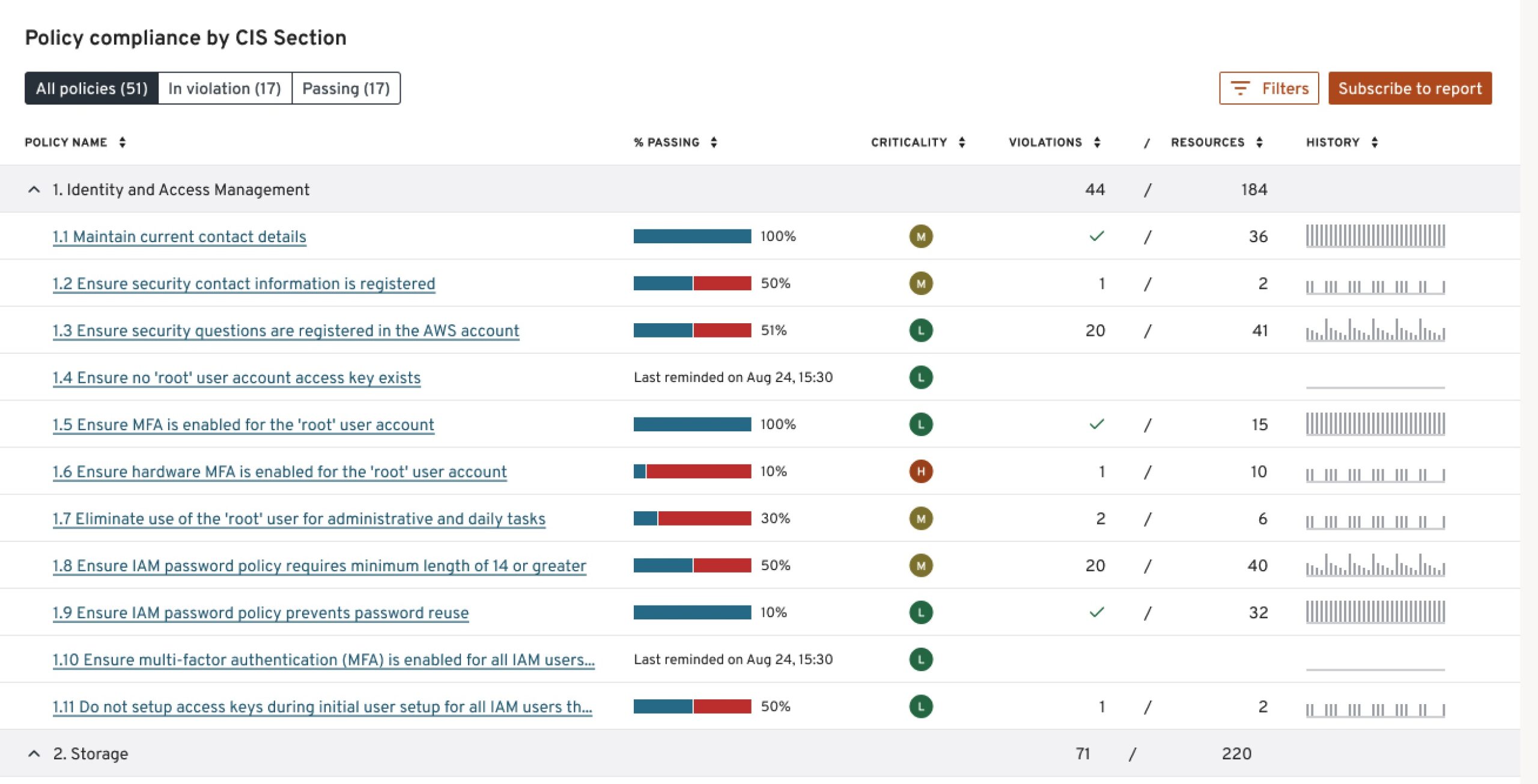
For example, the screen capture below reveals an organization’s compliance posture, broken out by each section of CIS policies. You can also view the status by resource type, severity, or line of business (based on account tags).
________
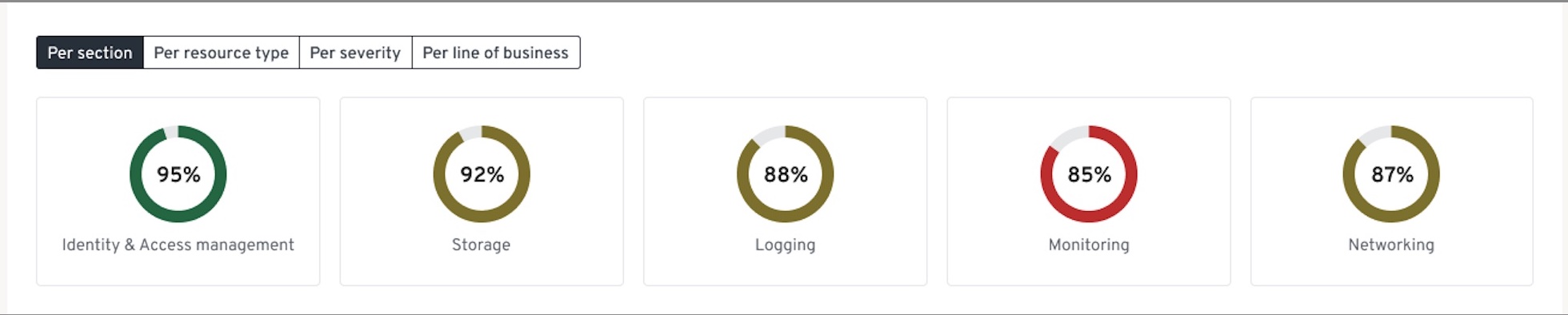
You can drill into each section to see the status of compliance with each policy, the number of violations, violation criticality, violation history, and more.
________
Automate Notifications and Remediation Workflows for Continuous Compliance at Scale
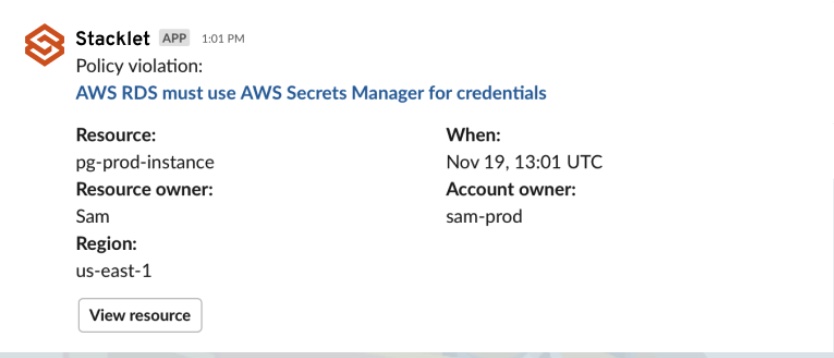
Stacklet Platform makes it easy for you to share a list of non-compliant resources with owners and teams to start the remediation process. Further, unlike other tools, Stacklet Platform enables you to take a proactive approach to fix issues. With Stacklet Platform’s simple, flexible policy language, you can automatically send notifications to the right team and trigger remediation workflows. In the event of policy violations, teams can be automatically notified through the channel of their choice, including Slack or email.
Depending on the nature of the violation, an automated action could immediately fix the non-compliant resource after warning the user. Alternatively, a Jira ticket could be opened, adding the action to the backlog of the engineering team. Anytime a change is made that leaves a resource non-compliant, the remediation and notification workflows can automatically be triggered, helping speed response. Taking a proactive and automated approach is critical to scaling compliance in the cloud.
Here is a sample policy in Stacklet Platform that will find all users in an identity and access management platform whose console credentials have been identified as stale. If these credentials have not been used within a defined timeframe, they can be automatically deleted. A notification will then be sent to affected users.

Here is an example of a Slack notification.
________
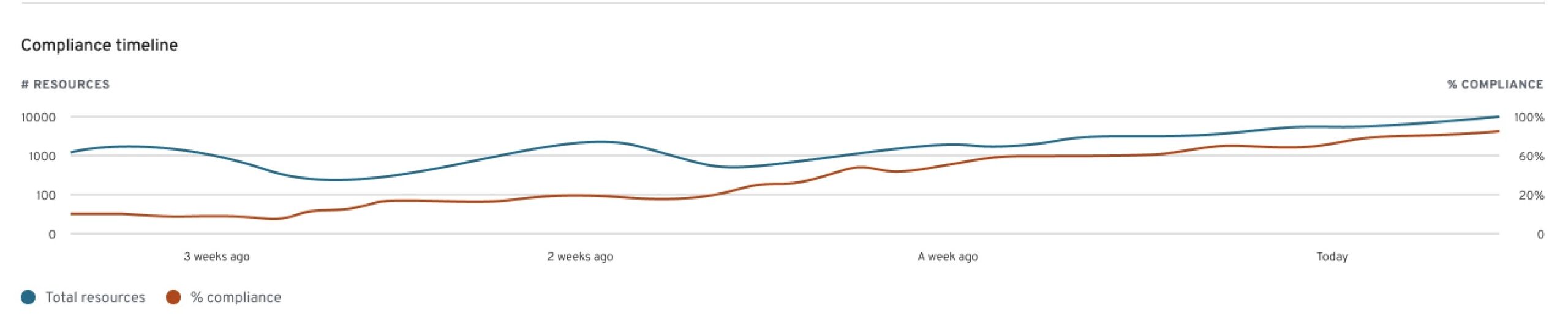
Stacklet Platform also provides insights into how your compliance status changes over time, which will help you understand if you are moving in the right direction.
________
Easily Meet Ever-Changing Compliance Needs Without Disrupting DevOps Workflows
Stacklet synchronizes all policy configurations and deployments changes, employing GitOps to enforce continuous governance. This process also ensures that policies are deployed independently of application code or Stacklet Platform updates. While Stacklet frequently provides updated policies, you can also add, edit, or adjust policies. This enables you to quickly adopt a new version of CIS or align with changing organization requirements or workflows.
Are you struggling to adopt CIS benchmarks in your organization? Schedule a demo here, and someone from our team can detail how Stacklet Platform can help.
Categories
- CIS
- cloud compliance
- Cloud Governance